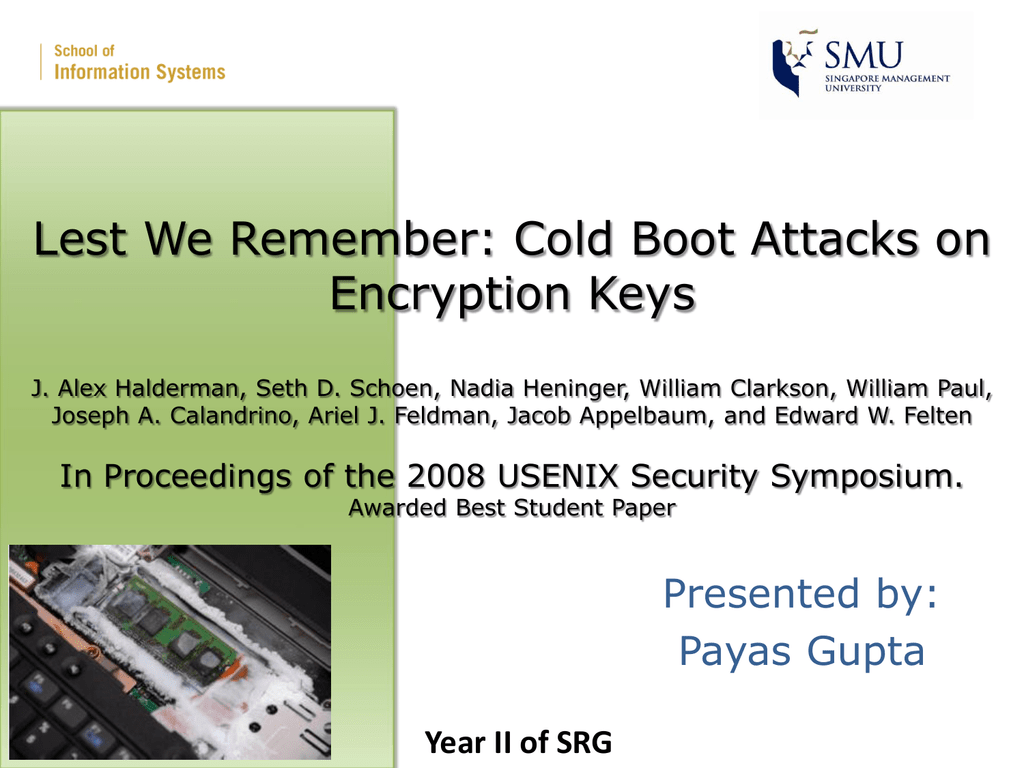
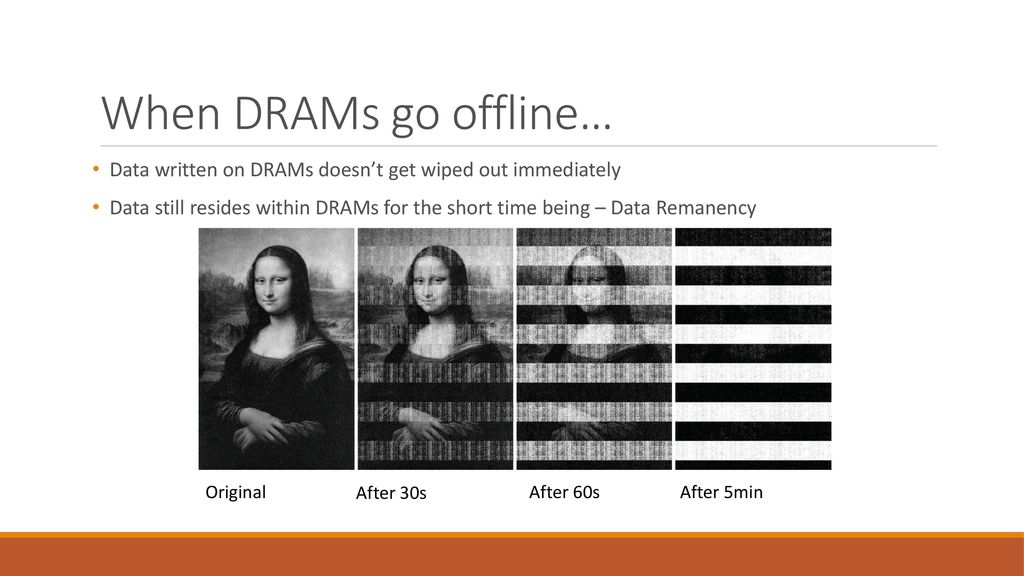
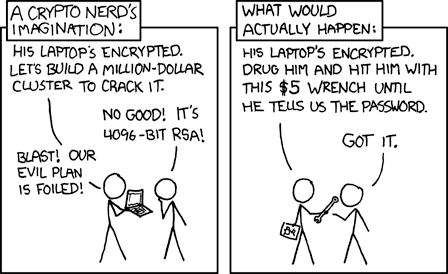
PPT – Lest We Remember: Cold Boot Attacks on Encryption Keys J. Alex Halderman, Seth D. Schoen, Nadia Heninger, William Clarkson, William Paul, Joseph A. Calandrino, Ariel J. Feldman, Jacob Appelbaum, and

Lest We Remember Cold-Boot Attacks Against Disk Encryption J. Alex Halderman, Seth D. Schoen, Nadia Heninger, William Clarkson, William Paul, Joseph A. - ppt download

PPT - Lest We Remember Cold-Boot Attacks Against Disk Encryption PowerPoint Presentation - ID:6627303



![PDF] Lest we remember: cold-boot attacks on encryption keys | Semantic Scholar PDF] Lest we remember: cold-boot attacks on encryption keys | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/31da09f829f14cd2c335f53b1f548bf5995967c5/9-Figure6-1.png)